Configuring API Manager
NextGenPSD2 Reference Toolkit contains TOML-based configurations. All the server-level configurations of the
API Manager instance can be applied using a single configuration file, which is the deployment.toml file.
Configuring deployment.toml¶
Follow the steps below to configure the deployment.toml file and set up the open banking flow for WSO2 API Manager.
-
Replace the
deployment.tomlfile as explained in the Setting up the servers section. -
Open the
<APIM_HOME>/repository/conf/deployment.tomlfile. -
Set the hostname of the API Manager:
[server] hostname = "<APIM_HOST>" -
Update the datasource configurations with your database properties, such as the username, password, JDBC URL for the database server, and the JDBC driver.
- Given below are sample configurations for a MySQL database. For other DBMS types and more information, see Setting up databases.
[database.shared_db] url = "jdbc:mysql://localhost:3306/openbank_govdb?autoReconnect=true&useSSL=false" username = "root" password = "root" driver = "com.mysql.jdbc.Driver"[database.apim_db] url = "jdbc:mysql://localhost:3306/openbank_apimgtdb?autoReconnect=true&useSSL=false" username = "root" password = "root" driver = "com.mysql.jdbc.Driver"[database.config] url = "jdbc:mysql://localhost:3306/openbank_am_configdb?autoReconnect=true&useSSL=false" username = "root" password = "root" driver = "com.mysql.jdbc.Driver"[[datasource]] id="WSO2UM_DB" url = "jdbc:mysql://localhost:3306/openbank_userdb?autoReconnect=true&useSSL=false" username = "root" password = "root" driver = "com.mysql.jdbc.Driver" -
Update the following configurations with the hostname of the Identity Server.
[apim.key_manager] service_url = "https://<IS_HOST>:9446${carbon.context}services/"[apim.key_manager.configuration] ServerURL = "https://<IS_HOST>:9446${carbon.context}services/" -
Update the hostname of the Identity Server in the following configuration:
[open_banking.gateway] consent.validation.endpoint="https://<IS_HOST>:9446/api/openbanking/consent/validate" -
The
frequencyPerDayvalue is sent in the consent initiation request body to indicate the requested maximum frequency for access without PSU involvement per day.- This enables request throttling according to the
frequencyPerDayvalue provided in accounts initiation request. - For a request to be throttled, the TPP should initiate the request.
a. To configure the custom throttling policy, enable the following configuration:
[open_banking_berlin.consent.freq_per_day] enable = trueb. Deploy the throttling policy located in
<WSO2_OB_APIM_BERLIN_TOOLKIT_HOME>/repository/resources/frequencyPerDayPolicyas a custom throttling policy in the Admin Portal of WSO2 API Manager.Note
- Set the Throttle Key as follows:
$customProperty.accountId:$customProperty.consentId:$userId:$customProperty.consumerKey - Set the Siddhi Query provided in the
<WSO2_OB_APIM_BERLIN_TOOLKIT_HOME>/repository/resources/frequencyPerDayPolicyfile.
See API Manager Documentation for the instructions.
- This enables request throttling according to the
-
The supported signature algorithms and digest algorithms are used in
SignatureValidationExecutorto perform signature verification and digest validation.- You can configure them using the following configurations.
- You can configure any number of algorithms by separating them using a comma.
-
By default, the following values are configured:
[open_banking_berlin.gateway.signature_verification] supported_hash_algorithms = ["SHA-256", "SHA-512"] supported_signature_algorithms = ["SHA256withRSA", "SHA512withRSA"]
-
By default, the following regex is used to validate the Organization ID:
^PSD[A-Z]{2}-[A-Z]{2,8}-[a-zA-Z0-9]*$You can override the above and use your own regex when validating the Organization ID of the TPP application. Configure the required regex as follows:
[open_banking.berlin.keymanager.org_id_validation] regex=”<CUSTOM_REGEX>”For more information, see Customize Consumer Key Validation
-
Replace the existing
com.wso2.openbanking.accelerator.gateway.executor.impl.consent.ConsentEnforcementExecutorconfiguration with the below configuration for all Accounts, Payments, and Funds Confirmations executor types.[[open_banking.gateway.openbanking_gateway_executors.type.executors]] name = "com.wso2.openbanking.berlin.gateway.executors.BerlinConsentEnforcementExecutor" priority = 7Note
- Add this executor before
com.wso2.openbanking.berlin.gateway.executors.ErrorHandlingExecutor. - Update the priority of the executor accordingly.
- Add this executor before
Starting servers¶
-
Go to the
<APIM_HOME>/bindirectory using a terminal. -
Run the
wso2server.shscript as follows:./api-manager.sh
Configure Identity Server as Key Manager¶
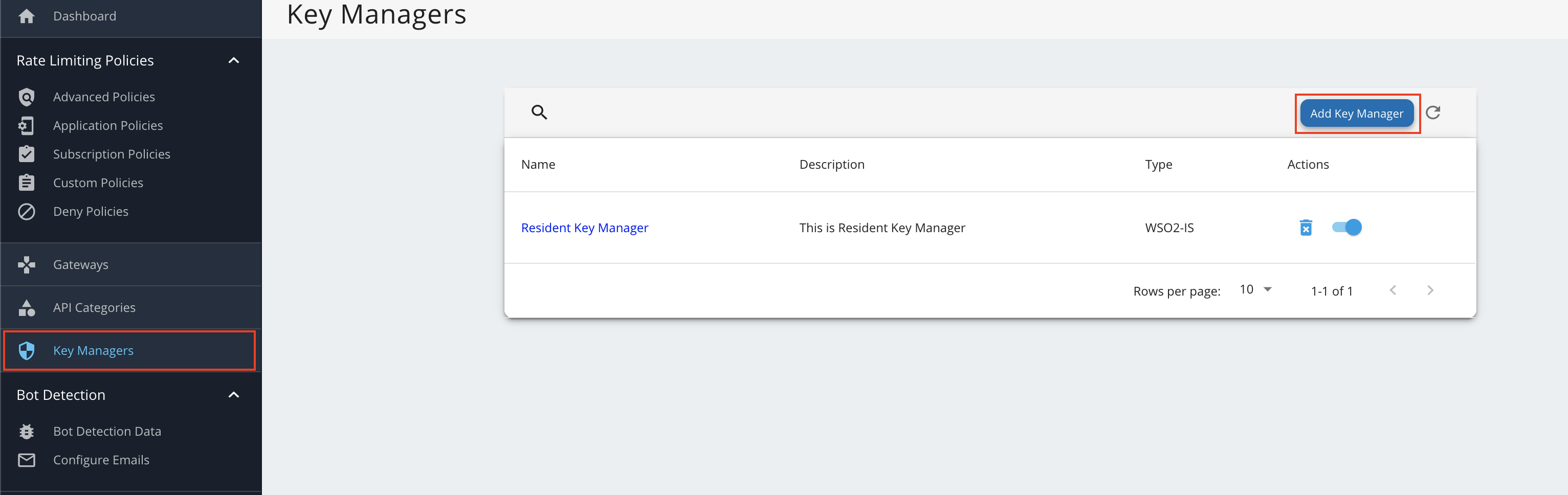
- Sign in to the Admin Portal of API Manager at
https://<APIM_HOST>:9443/admin. - Go to Key Manager on the left main menu.
-
Click Add New Key Manager and configure Key Manager.
Click here to see the full list of configurations...
Configuration Description Value Name The name of the authorization server. OBKM Display Name A name to display on the UI. OBKM Description The name of the authorization server. (Optional) Key Manager Type The type of the Key Manager to be selected. Select ObKeyManagerWell-known-url The well-known URL of the authorization server (Key Manager). https://<IS_HOST>:9446/oauth2/token/.well-known/openid-configurationIssuer The issuer that consumes or validates access tokens. https://<IS_HOST>:9446/oauth2/tokenKey Manager Endpoints Client Registration Endpoint The endpoint that verifies the identity and obtain profile information of the end-user based on the authentication performed by an authorization server. https://<IS_HOST>:9446/keymanager-operations/dcr/registerIntrospection Endpoint The endpoint that allows authorized protected resources to query the authorization server to determine the set of metadata for a given token that was presented to them by an OAuth Client. https://<IS_HOST>:9446/oauth2/introspectToken Endpoint The endpoint that issues the access tokens. https://<IS_HOST>:9446/oauth2/tokenRevoke Endpoint The endpoint that revokes the access tokens. https://<IS_HOST>:9446/oauth2/revokeUserinfo Endpoint The endpoint that allows clients to verify the identity of the end-user based on the authentication performed by an authorization server, as well as to obtain basic profile information about the end-user. https://<IS_HOST>:9446/oauth2/userinfo?schema=openidAuthorize Endpoint The endpoint used to obtain an authorization grant from the resource owner via the user-agent redirection. https://<IS_HOST>:9446/oauth2/authorizeScope Management Endpoint The endpoint used to manage the scopes. https://<IS_HOST>:9446/api/identity/oauth2/v1.0/scopesConnector Configurations Username The username of an admin user who is authorized to connect to the authorization server. Password The password corresponding to the latter mentioned admin user who is authorized to connect to the authorization server. Claim URIs Consumer Key Claim URI The claim URI for the consumer key. (Optional) Scopes Claim URI The claim URI for the scopes (Optional) Grant Types The supported grant types. According to your open banking specification, add multiple grant types by adding a grant type press Enter. For example, refresh_token,client_credentials,authorization_code.(Optional) Certificates PEM Either copy and paste the certificate in PEM format or upload the PEM file. (Optional) JWKS The JSON Web Key Set (JWKS) endpoint is a read-only endpoint. This URL returns the Identity Server's public key set in JSON web key set format. This contains the signing key(s) the Relying Party (RP) uses to validate signatures from the Identity Server. https://<IS_HOST>:9446/oauth2/jwksAdvanced Configurations Token Generation This enables token generation via the authorization server. (Mandatory) Out Of Band Provisioning This enables the provisioning of Auth clients that have been created without the use of the Developer Portal, such as previously created Auth clients. (Mandatory) Oauth App Creation This enables the creation of Auth clients. (Mandatory) Token Validation Method The method used to validate the JWT signature. Self Validate JWT The kid value is used to validate the JWT token signature. If the kid value is not present, gateway_certificate_aliaswill be used.(Mandatory) Use introspect The JWKS endpoint is used to validate the JWT token signature. - Token Handling Options This provides a way to validate the token for this particular authorization server. This is mandatory if the Token Validation Method is introspect. (Optional) REFERENCE The tokens that match a specific regular expression (regEx) are validated. e.g., [0-9a-fA-F]{8}-[0-9a-fA-F]{4}-[1-5][0-9a-fA-F]{3}-[89abAB][0-9a-fA-F]{3}-[0-9a-fA-F]{12}(Optional) JWT The tokens that match a specific JWT are validated. Select this icon CUSTOM The tokens that match a custom pattern are validated. (Optional) Claim Mappings Local and remote claim mapping. (Optional) -
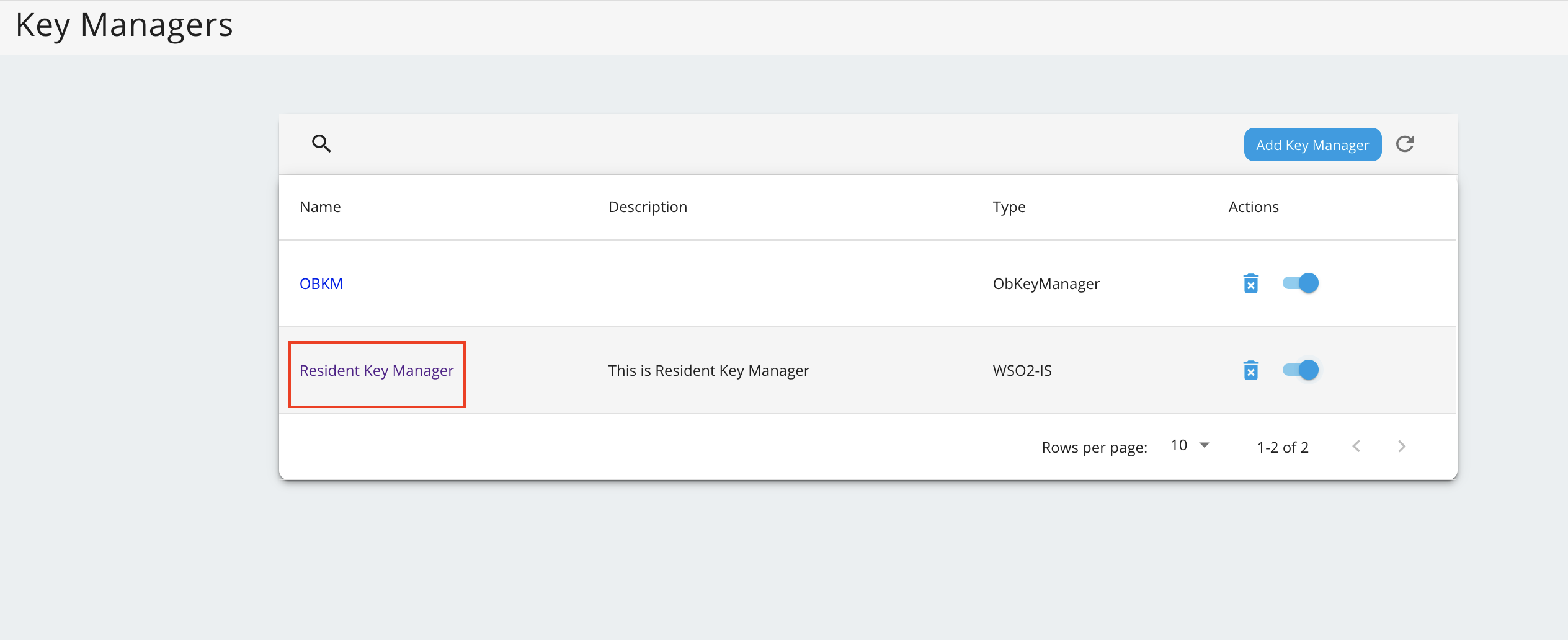
Go to the list of Key Managers and select Resident Key Manager.
-
Locate Connector Configurations and provide a username and a password for a user with super admin credentials.
-
Click Update.
-
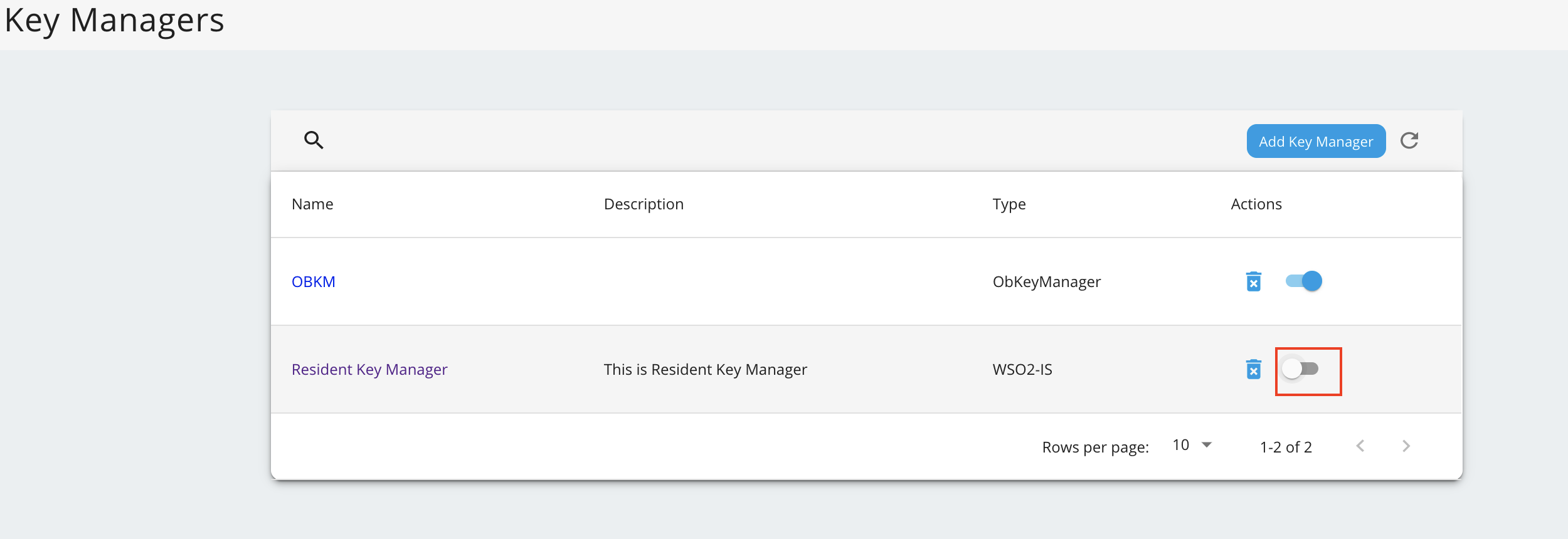
Disable the Resident Key Manager.